Threat actor APT28 targets Cisco routers with an old vulnerability
[ad_1]
The U.S., Europe and Ukraine are reportedly targets in this malware threat. Learn how to protect affected Cisco routers.
Threat actor APT28 is exploiting an old vulnerability in Cisco routers using Simple Network Management Protocol versions 1, 2c and 3 to target the U.S., Europe and Ukraine. This security threat is detailed in a recently published joint advisory from the U.K. National Cyber Security Centre, the National Security Agency, the Cybersecurity and Infrastructure Security Agency, and the Federal Bureau of Investigation.
SEE: Keep your business’s devices secure with this Mobile device security policy from TechRepublic Premium.
Jump to:
How is APT28 accessing Cisco routers?
The advisory states that in 2021, APT28 used malware to exploit an SNMP vulnerability, known as CVE-2017-6742, that was reported and patched on June 29, 2017, by Cisco. To successfully exploit that vulnerability, the attacker needed to know the router’s SNMP community strings, which are like passwords allowing access to the router’s data.
In addition to the joint advisory, the NCSC published a malware analysis report entitled Jaguar Tooth, which provides details on the malware deployed by APT28 using the SNMP vulnerability. The vulnerability is triggered to write the Jaguar Tooth code into the memory of targeted Cisco Internetworking Operating System routers before being executed.
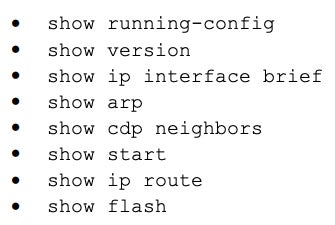
According to the NCSC, Jaguar Tooth is made up of payloads and patches that provide unauthenticated backdoor access, allowing the attacker to log in to existing local accounts. It also creates a new process called Service Policy Lock that automatically collects information and exfiltrates it over the Trivial File Transfer Protocol. The collected information includes device details, running configuration, firmware version, directory listings, and network information such as Address Resolution Protocol tables, interfaces and other connected routers (Figure A).
Figure A
Who is APT28?
APT28 is a threat actor that has been active since 2004; it also goes by the aliases Sofacy, Fancy Bear, Pawn Storm, Sednit, Tsar Team and Strontium. APT28 has been described as the military unit 26165 of Russia’s Military Intelligence Agency, previously known as GRU. Some of its members were charged by the U.S. Department of Justice in 2018 for “international hacking and related influence and disinformation operations,” according to a press release from the Justice Department.
The group is described in the Mueller special counsel investigation as “a cyber unit dedicated to targeting military, political, governmental, and non-governmental organizations outside of Russia, including the US.” And APT28 has departments with different specialties, including a malware development department and one conducting large-scale spear phishing campaigns.
Who has APT28 targeted with this vulnerability?
APT28 targeted Cisco routers in Europe, U.S. government institutions and approximately 250 Ukrainian victims, according to the report.
It is highly probable that some companies still use Cisco routers that are not patched or even in their end-of-life period. Such versions of Cisco routers are vulnerable to this exploit.
How to mitigate this Cisco router vulnerability
In a blog post about state-sponsored attacks targeting global network infrastructures, Cisco Talos reminds people that carefully selected SNMP community strings will block this attack, since the exploitation of CVE-2017-6742 needs the attacker to know the community string.
Cybersecurity company Talos, belonging to Cisco Systems Inc, reminds people that even well-chosen strings are transmitted in clear text if not using SNMP v3 and could be intercepted by a threat actor as SNMP older versions v1 and v2c lack proper encryption and authentication, while v3 relies on SSH and HTTPS protocols. It is, therefore, strongly advised to deploy SNMP v3 and encrypt all monitoring and configuration traffic and select complex community strings.
Other security prevention steps to take are also recommended:
- Modify default credentials on routers to unique and strong ones that are only known by administrators.
- Disable SNMP if remote management of routers isn’t necessary at your company in order to reduce the attack surface.
- Use modern — not end-of-life — hardware and software and keep routers up to date and patched.
- Configuration or behavior changes in routers should be monitored by tools based on TACACS+ and Syslog protocols.
- Implement strong policies using role-based access control. Only allowed personnel should be able to access the administration or configuration of these devices.
Disclosure: I work for Trend Micro, but the views expressed in this article are mine.
[ad_2]
Source: News
